Broadband Toolkit
Regional Planning Efforts
November 20, 2013Housing Advocacy Network
November 20, 2013
Overview
Do you work with residents of affordable housing? Are computers and the Internet part of your job responsibilities (even if they’re not part of your job description)? If you answered yes to both, this guide is for you.
The digital divide is a real concern, and to address it, many affordable housing developers are providing access to the Internet at their buildings for the residents. Sometimes this means computer rooms, other times it means direct connection to the Internet in each unit. This has meant that affordable housing staff now need to have basic knowledge of the technology that comes with providing Internet access.
When NPH first started to work on the toolkit, we conducted a survey of our housing developers to find out what their biggest challenges were. We wanted to make sure that the toolkit we built would be useful in addressing these challenges.
The purpose of this toolkit is to help non-technical staff of affordable housing organizations understand the landscape of broadband technology options, best practices, and available resources. This toolkit is NOT a comprehensive guide to everything about technology cost and service, and it is not a solution to the challenges that many organizations face to find funding for technology. What it IS, is a guide to figuring out solutions for the day-to-day challenges.
If you are like many people who will use this toolkit, you will still feel frustrated about the lack of available funding for broadband in affordable housing. You can do something about it! You and your organization can advocate for solutions that will not only support wiring a building for high-speed Internet, but also fund the continuing technology needs – software, computers, trainers, IT support, staff time – that it takes to help your residents really benefit. Here are some suggestions:
- Endorse Smart Housing and Broadband Access Principles and Priorities. Print this letter on your company letterhead and return it to NPH (email: oo@nonprofithousing.org; fax: 415-989-8166; mail: 369 Pine St., Suite 350, San Francisco, CA 94104).
- Urge capital funders to allow Internet services in the operating budget.
- Urge utility providers to offer discounted services and allow for exceptions to their non-compete provisions for nonprofits.
- Start discussions about considering broadband a utility like phone connection.
- Check out the California Broadband Initiative
- Check out unfunded FCC initiatives and if you like them, advocate that they be funded:
- FCC Broadband Plan (Connect America Fund)
- Digital Literacy Corps
You may also want to join our Property Stewardship Working Group or our Resident Services Roundtable, whose members have shared their time, expertise, and feedback on the toolkit. In addition to helping their residents bridge the digital divide, these two working groups also work on other policy and advocacy issues that support healthy buildings and communities.
Commit Resources
Success Story
Back in 2004, Deborah Estrada was one of the first Digital Connectors – a program that identifies talented young people and trains them in technology, with the requirement that they give back to their communities what they have learned. She was a freshman in high school from a low-income, immigrant family, and she didn’t know much about computers… Read More >>
As you make an organization-wide commitment to supporting access to broadband technology for your residents, don’t forget to commit the necessary resources to make that happen.
- Include broadband access in your organization’s strategic plan. Include support for technology – training, equipment, and staffing – and pay attention to organizational capacity.
- If you already have broadband in some developments, consider taking the service to scale organization-wide.
- Develop a broadband plan, and involve frontline staff in development of the plan.
- Standardization of programming and equipment will save you money, reduce burden on IT staff, avoid compatibility problems, and allow your organization to buy in quantity.
- If your organization has an IT person on staff, his or her responsibilities with regards to broadband for residents should be clearly articulated in the job description.
- Measure the impact of providing broadband access, such as resident usage rates.
- If you are including Internet services because your capital funder required it (TCAC or AHP, for example), beware. Providing these services without real organizational support will not serve your organization’s mission.
- Consider who is responsible for helping residents with their broadband technology issues: Resident services coordinators? Property management staff? IT personnel? All of the above? Ensure each know their roles and have access to the support and training they need.
- If you are a national organization, make sure that local staff have back-end support for technology purchased through contracts.
Involve Residents
Before implementing broadband on the sites, polling your residents will help to determine their needs and interests and manage expectations. Engaged residents will be committed to the security and success of your organization’s broadband investments, and it will help to build community at your buildings.
Conduct a Resident Technology Needs Assessment
- Collect data: demographics, computer skill level, computer access at work and home, interest in activities, personal technology goals, scheduling/availability.
- Distribute your survey at a monthly meeting, as part of another program, as part of annual recertification, as a raffle or with an incentive, or online.
- Use the results to determine goals.
Set Expectations
If your Internet is currently free but residents may have to pay for continued service in the future, make sure you’re communicating with residents to set expectations.
Bandwidth restrictions can mean that residents’ Internet connection is not ideal for streaming video. Make sure they understand what the service can do and what its limitations are.
Build a Community Steering Committee
Your committee should include residents, the tenant’s council, the property manager, and staff members. Invite the key players and informal leaders in the resident community. Consider offering a stipend to committee members. Use the committee to set technology goals for the property.
Examples of goals: Increase the number of residents who know how to use computers by providing basic instruction. Improve academic support for students by offering afterschool homework help 2 days a week. Make sure goals are SMART: Specific, Measurable, Attainable, Relevant, Timely
Make it visible!
Publicize all technology programming on one simple flyer and post and distribute it widely. Post signs on desks, monitors, and the wall of computer labs outlining resident guidelines.
Use Volunteers
Tejal Shah, Resident Services Supervisor at East Bay Asian Local Development Corporation (EBALDC) has been working with volunteers for years. All of EBALDC’s computer classes are run by volunteers or partners.
With limited staff, volunteers are a great way to provide technology support to your residents.
- Build relationships with service learning or internship programs at high schools and colleges. Many students are required to complete a certain number of volunteer hours as part of their programs.
- Recruit resident volunteers. Residents care about their homes and neighbors, and the benefits will be mutual.
- Get Americorp/City Year or another year long volunteer
- Check out Hands on Bay Area a volunteer clearinghouse. Other volunteer websites include Volunteer Center and VolunteerMatch. Some organizations also use Craigslist and Idealist.
Make sure that volunteers are properly trained, oriented and screened. Some organizations conduct background checks on volunteers. For maximum accountability, think of volunteers as staff of your organization who are not paid.
- Commit appropriate staff time to volunteer management. Kami Griffins of CTN recommends 10 hours/week minimum for someone managing the computer center, including managing the volunteers. This could be 10 hours/week of staff time, or an advanced volunteer or intern who is responsible for volunteer management. “Ideally, this would be a full time position, but 10 hours/week with the right person can ensure some consistent programming.”
- Think outside the box when it comes to types of volunteers. Volunteers come with all kinds of skill sets. They could be instructors/trainers, computer tutors, lab assistants, or help with community engagement, or with administrative tasks.
Offer Free Space to a Service Provider
“At the beginning,” says Martin Ugarte, Site Services Director at Valencia Gardens, “we didn’t have any experience putting together a computer lab. CTN was very helpful. They recruited volunteers and began offering classes.”
One way to increase your services capacity is to partner with a service provider. You can offer discounted or free space in exchange for service provision to residents. To protect the interests of both parties, and to ensure stability, keep the following points in mind:
- The partnership should be formalized with a contract or Memo of Understanding (MOU). For an example of a standard MOU see npgoodpractice.org.
- It’s important to make sure that your partners have sufficient financial support beyond the ability to save on rent. Look into the possibility of both organizations seeking funding or writing grants together in a way that could be mutually beneficial.
Other Possible Partners
SAN FRANCISCO DEPARTMENT OF TECHNOLOGY
This video explains how the SF Department of Technology is providing free internet services to affordable housing developments using city infrastructure, as well as other organizations working on internet access in San Francisco.
In addition to IT-related service providers, there are other possible partners that could be helpful to you. Here are some suggestions for other possible partners.
- Check to see if you have a municipal or county IT department. They may have assets such as fiber or a radio tower that could help you bring free or low-cost Internet services to your buildings.
- Other possible partners you should investigate: businesses, your local chamber of commerce, economic development organizations, community service organizations, cultural groups, educational organizations and institutions, ethnic organizations, family services organizations, financial institutions, legal organizations, media organizations, organizations serving people with disabilities, professional groups, religious organizations, senior centers, technology experts, youth organizations, women’s centers.
- Partnerships will bring additional resources to your residents and can be mutually beneficial for all parties involved.
Asset/Property Manager Checklist
“Broadband becomes a service that you are offering so if or when it goes down you have to get it back or you will have people that get more upset than if the toilet is not working”
-Survey Respondant
As a property and/or asset manager, you are responsible for the long-term financial stewardship of your building(s). These are areas to consider as a property/asset manager regarding broadband service provision.
Devise a method for securing computer your lab: security camera, alarms, key card access, cables and locks, staff/volunteer monitoring, resident involvement in accountability
Build equipment repair and replacement into the budget.
- Total Cost of Ownership (TCO) is a business concept that can be a helpful way to think about the cost of technology over time. TCO incorporates computer hardware and programs, installation and operation expenses, tech support, and long-term expenses such as maintenance and replacement. According to Tech Soup, “Some experts estimate that the purchase price of a new technology is closer to 10 or 15 percent of the long-term cost.” Check out this article about TCO.
- When creating your technology budget, plan for multiple years and the life (in years) of each component. For example, you could budget a desktop computer as having a life of 3-5 years.
Don’t forget to budget in the staff time and training that maintaining technology will require. - Consider the cost associated with unplanned repairs and maintenance for your broadband technology. One survey respondent, a property manager, budgets $500 per year for unplanned IT consulting for the computer lab.
Incorporate technology into property management goals, with regular ways to measure outcome and ways to provide clear feedback
Consider how technology in your property impacts your rule enforcement responsibilities. Be clear with residents about the consequences for technology rules and how they will be enforced. Make sure technology rules are communicated clearly, not buried in the house rules.
Consider your property’s technology needs when making personnel decisions, including when you write job descriptions.
Developer Dos and Don’ts
THINGS TO CONSIDER WHEN EVALUATING A VENDOR PROPOSAL
- Does it include ongoing maintenance and support?
- What is the installation cost?
- What is the bandwidth and could it be increased in the future?
As a project manager, you are responsible for all aspects of the development process, including meeting capital funder requirements and financial structuring. The following are important points to consider as you plan for broadband service provision:
DO endorse Smart Housing and Broadband Access Principles and Priorities. CETF Principles Priorities Print this letter on your company letterhead and return it to NPH (fax: 415-989-8166; email: Hilda@nonprofithousing.org; mail: 369 Pine St., Suite 350, San Francisco, CA 94104).
DO plan for Internet use from the very beginning of the process-before conduit planning, before the low voltage design plan, and before ANY construction takes place.
- Ask yourself, “Do I have the right stuff in there before the walls get closed?”
- The electrical engineer is NOT an IT expert. The internet piece usually falls to the low-voltage subcontractor of the electrician. Wiring for effective residential internet is not the same as general wiring systems.
DO involve the internet provider/installer in physical planning.
DO plan for future capacity. Include the infrastructure for future broadband services even if you don’t have the funds to pay for service now.
DO use rehab as an opportunity for adding broadband to an existing building. Both the physical rehab and the refinancing are an opportunity to put in the infrastructure and the operating budget to make broadband work.
DO think of wiring for Internet as a part of network engineering. Many aspects of building operations can be wired and networked together: security, fire alarm coordination, utility monitoring, temperature control, phones, etc. Some developers are using Internet telephone service to save on phone bills. Others are networking common areas to provide remote access for employees to network. Ask yourself, “How can my property be most efficiently built and designed for low-cost operation?” Once you are well networked, anything is possible.
DON’T assume that internet service providers (ISPs) or local exchange carriers (LECs) provide the means to distribute internet to your residents
- If you call a LEC and they quote you a per door price or the cost of a business grade circuit with enough bandwidth for the whole building, they are NOT planning to provide you with the network switch or other things you need to get the internet service to your residents.
DON’T sign over ownership of your wiring
- Make sure the agreement you sign with your internet installer does not give them ownership over the wiring in the walls. If you let your LEC/ISP pay for your conduit, it belongs to them and you would have re-install it to use another provider. It limits your and your residents’ options.
Resident Services and Broadband
“Internet access on an individual basis can be expensive. We would like to see everyone have access to the Internet at home and not have to choose between paying rent, other bills, or going to the grocery store. Also it may help their children learn as well as help with their own education. There could be a hundred reasons why to do it and I cannot think of very many reasons not to.”
-Survey Respondant
These tips are to help resident services providers integrate broadband with what they already do and make their jobs easier.
Be inclusive about Technology.
Don’t forget any of your resident populations including seniors, special needs residents-including people with vision issues, non-English speakers etc.
- Seniors might enjoy a class on how to use email or Facebook. Some organizations have installed brain fitness software for seniors with positive results.
- People with disabilities are less likely than other adults to use the Internet. Consider Universal Design principles when designing your computer lab so that disabled residents can access it, even if you don’t currently have disabled residents.
The Center for Inclusive Design and Environmental Access can be a good resource.
- Target different populations and ability levels with a variety of Internet service offerings. It can be a challenge to offer classes that address different skill levels and language proficiencies. One possibility is cycling through levels and languages.
- You can select Internet browsing in residents’ primary language, and bookmark newspapers from their home country.
Use broadband as a tool to further your other service offerings.
- For example, if you are offering ESL or financial literacy, offer some relevent computer instruction as a part of the course.
- Teach your residents how to use free benefits screening software/websites to find out what benefits they are eligible for: www.benefitscheckup.org
- Use technology to promote financial empowerment. Teach online banking and bill payment. Wells Fargo has a free CD that teaches online banking.
Measure and record the impact of broadband on residents.
- If you have a very advanced evaluation process or you are required to, you can calculate a Return on Investment (ROI) for broadband provision.
Check out this post from Techsoup.
- Things you might want to document/measure: number of users throughout the day/week, Internet speed, reaction and satisfaction with classes/workshops, learning before and after, ability to apply learning.
Glossary
A measure of available or consumed data communication resources in bits per second usually expressed as kilobits per second (kbps), megabits per second (Mbps), or gigabits per second (Gbps). The relationship between the three measures is as follows: 1 kbps (kilobits per second) = 1000 bits per second 1 Mbps (megabits per second) = 1000 kilo bits per second 1 Gbps (gigabits per second) = 1,000 mega bits per second
The amount of Internet capacity that you will have to spread between your residents, the office, and the computer lab. The amount of bandwidth needed depends upon (a) the number of simultaneous users; (b) the types of activities undertaken (e.g., checking e-mail vs. streaming video), and; (c) the desired responsiveness (e.g., how long it takes for an average web page to load).
A variation on the wireless mesh model where the number of simultaneous users at a specified access point is artificially limited in order to maintain a predetermined level of network performance.
(See mesh network)
broadband
Broadband refers to the increase in bandwidth that accompanied the shift in Internet technology in the first decade of the 21st century. Earlier dial up Internet allowed for simple applications such as email and web browsing. Internet delivered through cable modems, digital subscriber lines, wireless technologies and fiber optic transmission allows for complex downloads of music, video, and data.
Refers to the technology that allows computer systems to connect to one another over small or great distances. A broadband connection does not necessarily imply a connection to the Internet, but the word has come to mean one way that people refer to Internet access.
Category 3 (CAT3) cable is a cable for carrying low-voltage signals and is found primarily in older residences with basic telephone service. CAT3 is often referred to as telephone wire.
Network communications cannot be carried out over CAT3 wires.
Category 5 (CAT5) cable is a twisted pair cable for carrying low-voltage signals. Twisted pair cables are used in structured cabling for computer networks such as Ethernet, as well as other signals such as telephone and video.
There are various categories of twisted pair cables with CAT5 being one of the most common in use today. In general, the higher the category number, the faster data can be transmitted over the wires. Higher category numbers can also allow for longer uninterrupted cable runs between locations. A special classification of CAT5 cable known as plenum cable is required in many construction projects because plenum cable does not give off toxic gases in a fire.
The Central Processing Unit (CPU) is the brains of the computer. It is also called the processor. It is an internal component of the computer where most calculations take place.
The CPU of a computer will tell you how fast it will work and how many things it can do at the same time.
An automatic configuration protocol used on networks that use the Internet protocol (IP). Computers that are connected to IP networks must be configured before they can communicate with other computers on the network (including the Internet). DHCP allows a computer to be configured automatically by a networking device called a DHCP server without the need for a human intervention.
There are two choices for assigning IP addresses. Addresses can be assigned manually or via DHCP. When an IP address is assigned manually, activity originating from the IP address can always be traced back to a specific source. IP addresses assigned via DHCP rotate between connected devices and a single device that connects to a network one day may not get the same IP address the next time it connects. As such, the use of DHCP makes it difficult to trace activity back to a specific originating device, and this makes it harder to identify the source of abuse on the network.
Digital Subscriber Line (DSL) is a system that uses telephone lines to allow you to connect to the Internet at high speeds. Current technology allows one pair of wires to carry both voice communications and data communications.
DSL services are available in most parts of the United States even in areas where other types of broadband services are not available. DSL services often have a maximum bandwidth lower than the minimum bandwidth of cable or fiber optic broadband services, and this limits the number of simultaneous users. DSL services are usually available to individual residents whose units are wired for telephone service with CAT3 cable.
Digital Subscriber Line Access Multiplier (DSLAM – pronounced dee-slam) allows telephone lines to make faster connections to the Internet. It is a network device, located in the telephone exchanges of Internet service providers, that connects multiple customer DSLs to the Internet using technology that allows one pair of wires to carry digital signals for dozens of individual users.
An older residential complex with CAT3 cabling running from the MPOE to each unit might be able to install at DSLAM at the MPOE in order to deliver DSL services to each unit without the need for placing any equipment in the units.
The most widely installed computer networking technology. The Ethernet protocol is specified in the Institute of Electrical and Electronics Engineers (IEEE) 802.3 standard. In modern installations, Ethernet installations use special grades of twisted pair wires (e.g., CAT5). The Ethernet protocol is also used in wireless networks.
A technology that uses glass or plastic fibers to transmit data using light. A fiber optic cable consists of a bundle of threads each of which is capable of transmitting messages modulated onto light waves.
The technology that allows high speed Internet to transfer large amounts of information without electronic interference.
A device or set of devices designed to permit or deny network transmissions based on a set of rules. Firewalls are used to protect networks from unauthorized access while permitting legitimate communications to pass.
A tool that can protect information on computers that are connected through a network. Firewalls can either be installed as stand-alone network devices, or as a software firewall that is installed on an individual computer. Failure to have a functioning firewall increases the risk of a computer or networking being maliciously exploited.
A software program or set of instructions programmed into a hardware device. It provides necessary instructions for how the device communicates with its various hardware components.
All computerized systems use firmware and, because firmware is a specialized form of software, there are occasions when firmware has to be upgraded or patched.
A generic term for making an identical image of a computer hard disk drive. Sometimes referred to as cloning, ghosting is a method of converting the contents of a hard drive, including its configuration settings and applications, into an image, and then storing the image in a secure location for future use. This image can be used to restore a computer to its original configuration if something goes wrong.
A useful tool for restoring computers in a computer lab in the case of damage.
A specific geographic location in which an wireless access point provides public wireless broadband network services to mobile visitors through a Wireless Local Area Network (WLAN). Hotspots may be password protected and are often located in heavily populated or frequented locations. Hotspots typically have a short range of access.
A generic term for a location from which a wireless signal emanates regardless of the type of wireless device generating the signal.
A common connection point for devices in a network. Hubs are used to connect segments of a LAN. A hub contains multiple ports. Hubs have been replaced by network switches.
Hubs are considered obsolete equipment.
An identifier for a computer or device on a network that uses the Internet Protocol (IP) as a means for allowing devices to communicate with one another. Networks using this protocol to route messages based on the IP address of the destination. IP addresses come in two different versions – IPv4 and IPv6. The format of an IPv4 address is a numeric address written as four numbers separated by periods (referred to a “dots”). Each number can be zero to 255. For example, 1.160.10.240 could be an IPv4 address. IPv6 is a newly released protocol which will be more broadly implemented in 2014.
There are private IP addresses that can be used on your LAN, and there are public IP addresses that must be used in the Internet.
A set of standards for digital transmission over ordinary copper telephone wire as well as other media. Home and business users who install an ISDN adapter (in place of a telephone modem) connect to the Internet faster than with a modem connection.
ISDN is an obsolete technology that is only used in areas where DSL is unavailable.
A company that provides Internet (broadband) services, including personal and business access to the Internet. For a monthly fee, the service provider usually provides a software package, username, password and access phone number.
The local Internet provider such as Comcast or AT&T that can provide Internet installation and service.
A Local Area Network (LAN) supplies networking capability to a group of computers in close proximity to each other such as in a multi-tenant residential building or office. A LAN is useful for sharing resources like files and/or printers. A LAN often connects to other LANs and/or to the Internet. A LAN can run over wires (e.g., CAT5) or can function without wires (i.e., a wireless LAN or WLAN).
A way to connect the computers in your computer lab to a shared printer, and one way to distribute Internet services.
A generic term for a public telephone company in the U.S. that provides local service. Alternately: Competitive Local Exchange Carrier (CLEC).
A LEC may directly provide broadband (Internet) services to end-users, or a LEC may sell some its bandwidth to other vendors, known as ISPs, who in turn resell Internet services to end-users.
An important consideration when setting up wireless links between sites
Might be necessary to distribute a wireless signal or when connecting networks housed in different buildings.
Media Access Control (MAC) Address is a hardware address that uniquely identifies each node of a network. Every network card (wired or wireless) is assigned a unique MAC address.
MAC addresses can be changed by users allowing one system to appear as a different system on a network. Even with this ability to “spoof” a MAC address, the MAC address is still used (at times) to limit the devices that can connect to a network.
A mesh network (or wireless mesh network) is a network that provides Wi-Fi connectivity within an urban or suburban environment. It is comprised of “mesh routers” which are a combination base station (hotspot) and router in one device. Also called “mesh nodes” the devices are typically installed in elevated locations near a power source.
A mesh network can provide uninterrupted wireless coverage throughout a residential complex. Planning for a mesh network is important since each mesh router (mesh node) requires power, and the mesh network must ultimately connect to a wired broadband connection.
Multiprotocol Label Switching (MLPS) is a way to integrate information that gives network operators flexibility to divert and route traffic around link failures, congestion, and bottlenecks.
MLPS is implemented by LECs.
Minimum Point of Entry (MPOE or MPoE — Pronounced em-poe) is the closest practical point where the cables of a telecommunications service carrier (i.e., LEC) cross a property line or where its wiring enters a multi-unit building.
The number and placement of your MPOEs will determine the cost of installation for a wired network in an existing building. MPOEs should be planned for in new buildings to allow for easy future network installation.
Used to connect multiple computers or other devices as part of a LAN. Network switches can be stand-alone units or integrated into a device like a router. Network switches can be unmanaged or managed. A managed switch contains firmware that allows an administrator to assign a maximum (or minimum) amount of bandwidth to a specific port on the switch.
If you have a LAN, you will need a network switch.
The term port can refer to either a physical or virtual connection point. Physical network ports including Ethernet, universal serial bus (USB), and parallel ports allow connecting cables to computers, network switches, routers, and other peripheral devices. Virtual ports are part of IP networking. They allow software applications to share hardware resources without interfering with each other. Computers and routers automatically manage network traffic traveling via their virtual ports. Network firewalls additionally provide some control over the flow of traffic on each virtual port for security purposes.
Ports control the flow of information over a LAN as well as to and from the Internet. Closing a port restricts the flow of data and can be used to limit what users can do (e.g., closing the ports used by video conferencing software on a network router would prohibit all users from using the service).
The ability to log onto a network from a distant location. The term remote control refers to taking control of another computer.
Remote access can help your IT specialist fix computers even if he/she can’t come into your computer lab or office.
A device that forwards data packets to their destinations, based on their IP addresses. Most modern routers also include a firewall and network switch.
A router will be installed between your LAN and the Internet. Additionally, a router can segregate the computer lab from offices, and a router (or routers) can also segregate individual residential units from one another.
Service Set Identifier (SSID) is a unique identifier attached to information sent over a WLAN that is displayed when a mobile device searches for a connection. It is the name of the WLAN, and all wireless devices on a WLAN must have the same SSID in order to communicate with each other.
Each device in a give locale that allows a user to connect wirelessly to a network must have a unique SSID.
A fiber optic or copper line that carries a large amount of data quickly, and is usually used for businesses that experience high volume and cannot afford to be offline or have their websites down.
T1 is a business class line that may or may not be necessary for your property.
Used by ISPs when abuse is detected on a network. Closing the throttle reduces the amount of bandwidth available to an end-user.
When a single broadband service connects an entire property, network abuse (e.g., downloading software illegally) can result in the ISP throttling down (i.e., reducing) the bandwidth for the entire property thereby impacting all residents.
Terms of service (commonly abbreviated as ToS or TOS and also known as Terms of Use, Terms & Conditions or Terms for short) are rules which one must agree to abide by in order to use a service. Unless in violation of consumer protection laws, such terms are usually legally binding. Terms of Service can also be referred to as Terms of Use or sometimes merely as a Disclaimer, especially regarding the use of websites.
This is important to read and understand before entering into any contract or purchasing any products/equipment. Violation of an ISPs TOS can result in the termination of broadband services.
Any wire (e.g., CAT5) where individual pairs of wires are twisted together at various intervals to reduce electronic interference.
A group of hosts with a common set of requirements that communicate as if they were attached to the same broadcast domain, regardless of their physical location.
A VLAN can be used to segregate individual residential units from one another.
A wireless standard for connecting electronic devices. A Wi-Fi enabled device such as a personal computer, video game console, Smartphone, and digital audio player can connect to the Internet when within range of a wireless network connected to the Internet. A single Wi-Fi hotspot has an average range of about 20 meters (65 feet) indoors. Wi-Fi has a greater range outdoors and multiple overlapping hotspots (i.e., a wireless mesh) can cover large areas.
Wireless Internet service can connect residents’ computers to the Internet without physically plugging into a wired network provided the residents’ computers have wireless networking capabilities.
The transfer of information between two or more points that are physically not connected. Distances can be short (e.g., a few feet as in a television remote control), or very long ranging from thousands to millions of miles for deep-space radio communications. The term wireless encompasses various types of fixed, mobile, and portable two-way radios, cellular telephones, and wireless networking. Wi-Fi is a specific type of wireless networking that allows for ease of configuration and connection between devices.
Typically radios that provide Internet access and broadcast an SSID, the name of the network (like SFHAwifi) Either a stand-alone device or one integrated into another networking device (e.g., a router) that allows other wireless networking enabled devices to connect to an established LAN or WLAN. (see hotspot)
A community room can generally be served by a single wireless access point. A large property with ubiquitous wireless service could have dozens of wireless access points installed.
Sometimes called a signal booster, a wireless amplified attaches to a router, access point, or Wi-Fi client at the place where the antenna connects. A wireless amplifier can be powered or unpowered, and it can provide for a directional wireless signal or non-directional wireless signal.
This can be used to amplify your wireless signal in order to get wireless service to residential units.
Radios that can extend a wireless signal around a property or a City. A property owner with several buildings could have one site that has Internet and with wireless bridges connect the other sites that can “see” (see LOS) the first building, if there are no obstructions. Specialized wireless networking equipment is required to create a wireless bridge.
A wireless bridge can be used to connect two or more buildings that are physically separated. The equipment must generally be place high up on the structure and be near an electrical power source.
Sometimes called “range expanders”, a wireless repeater is a stand-alone unit positioned within range of a wireless access point that serves as a two-way relay station for wireless signals. To boost signal strength of a wireless repeater, a wireless amplifier may be attached.
A Wireless Local Area Network (WLAN) is a type of local area network that uses high-frequency radio waves rather than wires to communicate between nodes.
Vendor and Resource Inventory
This list of links and organizations will give you a way to start exploring resources and organizations that can help your organization and residents better utilize broadband technology.
HARDWARE
- Ubiquiti sells wireless radios that can extend a wireless signal around a property, between buildings. Their radios cost between $60-$90.
- Meraki, Same as above, hardware is more expensive but easy to deploy and manage.
INSTALLATION/TECH SUPPORT
INSTRUCTION
- Community Technology Network, Check their resources page, it is full of tutorials in multiple languages and other great resources.
DONATION/DISCOUNTED PURCHASE
- Local Government
- Reliatech (a project of the Stride Center)
CURRICULUM
- GCFLearnFree.org has free online learning tutorials to improve technology skills (as well as literacy and math). A program of Goodwill Industries of Eastern NC, Inc.
- Hands on Banking is available in both Spanish and English and the program is offered free on the Internet for adults, young adults, and school-aged children without commercial content or product placement.
INFORMATION/OTHER
- Cnet for consumer and expert technology reviews
- Get Connected Today is fed information by 211 California and partner organizations.
- Tech Soup “Cookbooks” is for libraries but highly relevant to affordable housing organizations
- Tech Atlas helps nonprofits map out technology, with free and paid online tools
PRESENT FUNDING SOURCES
- CA PUC Teleconnect: Present has been used by affordable housing developers such as Abode Communities in Los Angeles (www.abodecommunities.org) for new construction. It provides for a 50% discount on T1 lines used by non-profits. Any phone or internet service provider in California should be aware of the Teleconnect Fund and be able to tell you what services apply. Please note that even with the discount, T1 lines are not always the most cost effective choice for every organization.
- USDA Rural Utilities Service (Present)
- Community Connect Grants
- Farm Bill Loan Program
OTHER ORGANIZATIONS/WEBSITES TO CHECK OUT
- Giant Rabbit, Vendor
- Monkey Brains,
Vendor
- Sonic.net, Vendor
- Telepacific, Vendor
- Wegowise, Vendor, helps affordable housing developers track and improve utility costs
- Baycat Center for Arts and Technology, Nonprofit,
- Next Step Learning Center, Nonprofit,
- Oakland Digital Arts and Literacy Center, Nonprofit,
- Stride Center, Nonprofit,
- Empowernet, Social enterprise of The Stride Center,
- Code for America, Nonprofit,
- Community Broadband Networks, Nonprofit
- Educase, Nonprofit
- Zero Divide, Nonprofit
- Wireless Future Project, Information/Other
- HUD Neighborhood Network Grants (Past), Past Funding Sources
- NTIA BTOP Program, Past Funding Sources
- Bridging the Technology Divide, Article
Downloads
Computer Lab Installation Checklist
Provided by Community Technology Network (www.ctnbayarea.org). This document offers recommendations for everything from layout, location and lighting to hardware, software and security. It is an excellent resource if you’re just beginning to consider creating a computer lab, or are under way and want to cover all of your bases.
Community Technology Network (CTN) works to bridge the digital divide through programs that support and enhance digital literacy in the Bay Area’s most vulnerable neighborhoods.
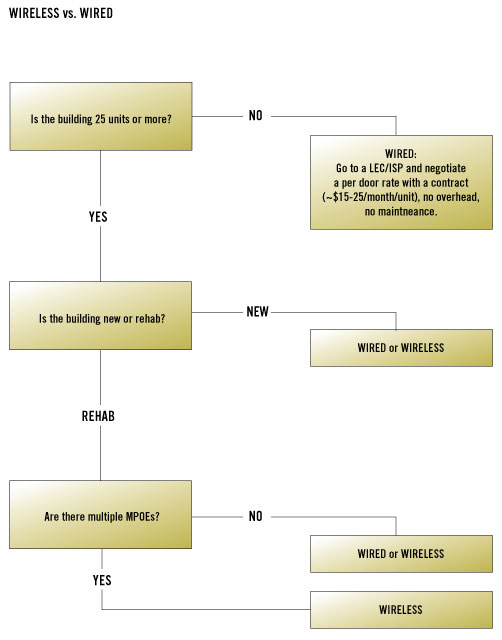
Wireless Vs. Wired Decision Matrix
If you’re wrestling with the decision between wireless and wired Internet service for your building or building, this decision matrix can help guide your thinking
Computer Lab Tips
“Some passwords for older (5-7 years) computer labs have been lost, which makes it much more time consuming and expensive to fix otherwise simple issues.”
–Survey Respondent
These tips will help you ensure that your computer lab operates continuously and securely by helping you balancing security settings and computer upkeep with the needs of your residents.
Plan smart:
Community Technology Network published a checklist which offers recommendations for everything from layout, location and lighting to hardware, software and security. It is an excellent resource if you’re just beginning to consider creating a computer lab, or are under way and want to cover all of your bases.
Wipe me clean:
Consider using a disk protection program like Steady State, Deep Freeze or another similar software that will wipe the computer after each use and protect against viruses, etc.
- Even with this type of program, some highly sophisticated viruses can get through, especially if the lab is being heavily used.
- Please note that Windows 7 is not compatible with Steady State. Until a replacement is created, there is no free alternative.
- Provide thumb drives to residents so that they can save documents. This is a low cost goodwill gesture that will help residents to understand the importance of protecting computer labs despite the inconvenience.
A ghost can be your friend:
Consider creating ghost CDs of the computers in your lab so that they can be recreated if any problems occur. Disc cloning creates a copy of the entire hard drive and can capture a particular configuration of software and operating system and then push that snapshot out to another computer with similar hardware components. Creating ghost CDs can be helpful when you buy a batch of new computers, to ensure standardization, to restore computers after they fail, and as a preventative maintenance and troubleshooting measure.
Some software to consider are:
- Symantec Ghost – Techsoup has a version that can be used with multiple computers in a network.
- Acronis True Image – creates full image back-ups.
- Windows 7 has a free, built in feature for the home edition called System Image. You can find it in the “Backup and Restore” feature. It will prompt you to put in a USB drive and backup an image of the computer, and it will compress the information. The program will automatically check to make sure there is enough room on the disc.
Create an online community:
Consider creating a portal webpage for each property where community information and events can be shared. You can create a property-wide intranet to share important forms such as work orders and recertification forms.
Refurbished is as good as new:
You can save money by buying refurbished computers . But if you do, be sure to pay attention to the following:
- Buy from a qualified refurbishing company.
- Pay attention to the warranty and return policy.
- Check the refurbisher’s “fail rate” or “return rate”.
- Find out what operating system (if any) you’ll get with the computer.
- Find out what peripherals (for example mice, keyboards, printers) are included.
- Make sure that the hardware is compatible with the software you’re going to use. If you’re not sure, ask your IT staff or consultant.
- Don’t be afraid to negotiate contracts with vendors.
How to deal with illegal downloading:
- Set the Rules: Make sure to develop lab rules (preferably with resident involvement) and an acceptable use policy that all users of the computer lab sign. Use this page and modify it as needed for your lab.
- It is important that residents know the consequences of illegal downloading. Make sure they understand that the Internet provider will notice and cut off service if illegal downloading is detected and continues. Emphasize that this has happened to other affordable housing properties.
- If you do get in trouble with your ISP for illegal downloading, some IT consultants have been able to identify and limit responsible IP addresses without identifying which units are causing the problem.
Write it down:
- Document and backup all license numbers, passwords and codes at the time of installation, especially if you are using an outside vendor. This will ensure that even if staff or vendors change, your organization is in control of all technologies purchased.
Be Creative
“We have one building that has wifi because it was being provided to an adjacent building and the equipment had to be placed on our building so we were able to negotiate that our tenants should and could use it too.”
-Survey Respondent
Before you decide on wireless or wired broadband for your buildings, it is important to weigh the pros and cons.
- Wireless Internet can be a bit cheaper than wired but the effectiveness will depend on the physical layout of your building. If you have scattered buildings with trees in between, for example, creating a wireless system that ensures good access throughout the property will be trickier than for a property where all units are close to a central location.
- Even a building that is not already wired for DSL can get a well functioning wired system. It is possible to use the existing wiring (used for telephone service.) Check first to see if you have multiple MPOEs. This solution is similar to when people run DSL over the phone line, but it can be done on a network-wide basis.
- Wireless can be complicated for residents to connect to on their personal computers vs. DSL where they can “plug and play.”
- Residents must have functioning wireless cards in their personal computer to connect. Often, they will think there is a problem with the wireless when the problem is really with their computer.
- Wireless networks can have password and ISP address issues that may sometimes make connecting to the network difficult, even when the signal is strong.
- Wireless can be fixed remotely by an IT specialist, if the network is set up to do that.
- Before speaking to an IT consultant about installing broadband, make sure you know the location of your MPOEs and existing wiring, servers, and routers.
- If you decide that you want to split a wired internet line to distribute throughout your building, make sure that your LEC/ISP allows it for that product.